As an entrepreneur, taking steps to safeguard your business is essential. In the contemporary business world, physical and digital risks threaten any business's assets, reputation, and future success.
Understanding these threats and implementing a robust strategy to combat them is not an option but a necessity— that's the purpose of this piece.
As you read this article, you'll learn insights from physical, digital, and internal threats to reinforce your business.
Take these steps, and your business will be far less likely to be compromised by a security breach.
In this article:
- Understanding Business Security Basics
- Essential Security Measures
- Establishing a Business Continuity and Disaster Recovery Plan
- Hiring Security Professionals
- Legal and Compliance Aspects of Business Security
Understanding Business Security Basics
Business security is the set of measures and strategies employed by a company to safeguard its assets. It involves protecting everything from physical assets such as machinery and office equipment to intangible assets like intellectual property, customer data, and company reputation.
A robust security plan addresses physical, digital, internal, and external threats and implements protective measures to prevent and mitigate them.
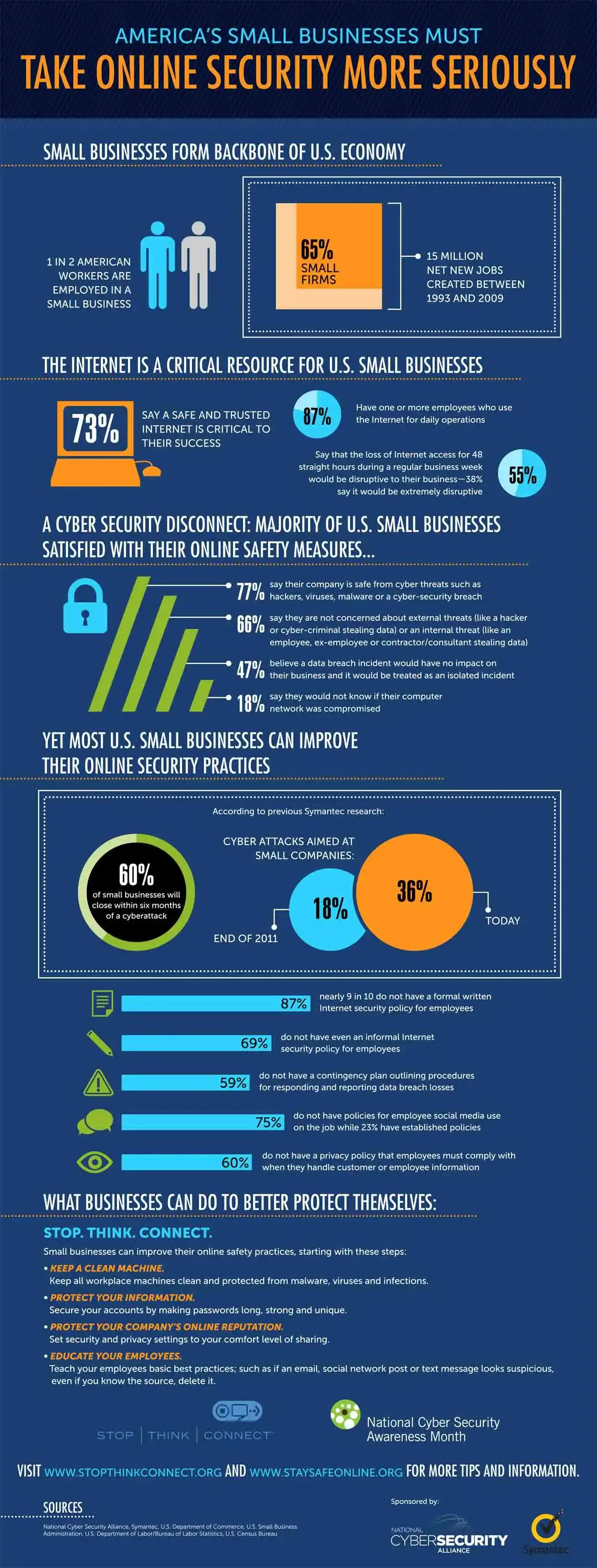
Source: Signix
Types of threats businesses face
The threats that can endanger a business will fall into several categories.
Cyber threats
Cyber threats are any potential or realized security breach that targets a business’s information system (digital software and hardware).
From phishing scams to ransomware attacks, annual cybersecurity breaches may cost companies as much as $10.5 trillion globally.
It's crucial for businesses to have a business insurance policy in place to mitigate the financial impact of such breaches.
Physical threats
Physical threats are security risks to physical property, such as theft, vandalism, or natural disasters, that can disrupt business operations or damage property.
Specialized insurance platforms like ContractorNerd can help business owners compare multiple quotes and secure tailored coverage that specifically addresses physical threats.
Internal threats
These threats come from within your organization. They could be intentional, such as an employee stealing sensitive information, or unintentional, such as an employee unknowingly opening a malicious email attachment.
External threats
External threats come from outside your organization, like competitors engaging in corporate espionage or criminals attempting fraud.
Potential consequences of inadequate security
On the surface, there's a risk of financial loss from theft, fraud, or data breaches. Then there's the operational disruption, which could halt business processes and result in missed opportunities or lost revenue.
It is mainly because consumers highly value their privacy and security, and even a single data breach can damage a company's credibility and customer trust beyond repair.
Understanding these basics is the first step to fortifying your business.
As we delve deeper into the essential security measures every entrepreneur should take, remember: your business's security is as strong as its weakest link. Aim for a comprehensive, well-rounded security plan that covers all bases.
Essential Security Measures
1. Physical security measures
If you operate out of an office or sell from a brick-and-mortar shop, ensuring the physical security of your business premises is fundamental to your overall security strategy. It involves safeguarding your assets, providing a secure environment for your employees, and handling certain payment types.
For example, knowing if a check is fake will save your business thousands of dollars. Here are some other key measures to consider:
Installation of surveillance cameras
Surveillance cameras act as your organization's eyes, constantly monitoring your premises. Ensure your cameras cover critical areas such as entrances, exits, and locations where valuable assets or important documents are stored.
Also, consider adopting the likes of Bold Group alarm monitoring software so that security devices, including power-over-ethernet cameras, can be tracked and analyzed in real-time for enhanced security management, equipping you to respond to any event swiftly and decisively by responsible team members.
One effective approach is to integrate a Coram AI camera system, which combines intelligent monitoring with advanced analytics to proactively detect threats and elevate on-site protection.
By integrating such solutions with unified endpoint management, you can ensure all devices are monitored and managed seamlessly, equipping responsible team members to respond to any event swiftly and decisively.
For businesses operating in low-light or nighttime environments, Coram’s night vision cameras offer an excellent solution. These advanced cameras provide clear visuals even in complete darkness, significantly boosting your after-hours security and deterring potential intruders.

Source: ButterflyMX
Secure locking systems
High-security locks and deadbolts offer the first line of defense against unauthorized access.
In recent years, electronic locks and keyless entry systems have gained popularity, allowing access only to individuals with the current codes or access cards.
These systems can be more secure and convenient, allowing you to easily control and monitor access to your premises.
Employee ID and access control
Implementing an employee identification system is essential in a secure business environment.
IDs allow for easy personnel identification, while systems like Automated Identity Verification can restrict unauthorized personnel from entering certain areas. It ensures that only individuals with the proper clearance can access sensitive areas, reducing the risk of internal threats.

Source: Avon
Regular security audits
Even the most robust security systems need regular check-ups. A security audit assesses your current security measures to identify potential weaknesses and areas for improvement.
Ensure your systems are up-to-date, functioning correctly, and effectively protecting your assets. Additionally, assessing your automatic gate openers can significantly bolster physical security.
It's also crucial to check fire systems with advanced testing solutions to ensure they function properly in emergencies.
For businesses considering updates or installations, evaluating systems like the Chamberlain vs Liftmaster wall mount offers insights into robust solutions tailored for modern security needs.
2. Cybersecurity measures
Depending on your type of business, cybersecurity risks, including ransomware protection, can be the most significant, as customer data and digital assets such as identity information and credit card details often form the backbone of many businesses.
Threat modeling can be particularly useful in addressing these risks by identifying potential threats and vulnerabilities.
One highly effective approach is leveraging cloud application security testing to ensure robust protection for your business's applications and systems.
Knowing how to protect your business from cyber threats is essential. Additionally, using a decentralized VPN can improve security and privacy by spreading data across multiple servers.
You can also educate your team more effectively with free cybersecurity infographics that simplify complex concepts into easy-to-understand visuals.
Regular software updates and patching
Developers frequently update their software to address security vulnerabilities.
Keeping your organization’s software up to date on an ongoing basis, along with robust patch management procedures, will help ensure your systems aren't left open to exploits that cybercriminals can leverage.
Be cautious about unsolicited contact from software developers, as tech support scams are a common form of cyberattack.
For businesses striving to enhance digital asset protection and streamline user account management, learning to effectively implement SCIM support can be a game-changer. This approach not only fortifies cybersecurity but also simplifies user access across various platforms.

Source: Clotech
Firewall and antivirus protection
By regulating incoming and outgoing network traffic, firewalls serve as an entrepreneur's first defense against cyberattacks.
If malicious programs make it through your firewall, antivirus programs protect your systems from malware that can steal, delete, or encrypt your data.
Data encryption
Encryption scrambles your data, turning it into a code that can only be deciphered with an encryption key. It means that even if a hacker breaches your data and obtains sensitive information without the encryption key, that information is worthless to them.
Secure password policies
Your business should have security policies requiring strong, unique passwords, and many organizations now rely on business password managers to securely store and manage employee credentials. These phrases combine uppercase and lowercase letters, numbers, and special characters.
Ensure your password policy requires employees to update their passwords regularly and avoid reusing them across multiple platforms.
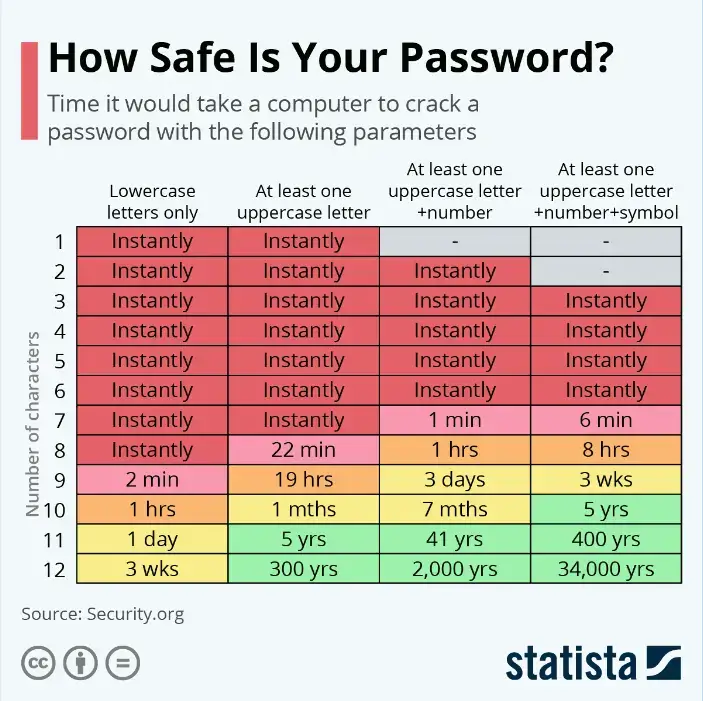
Source: Statista
Two-factor authentication
Two-factor authentication (2FA) adds an extra layer of security by requiring a second form of identification beyond just a password. It could be a fingerprint, a mobile app notification, or a unique code sent via text or email.
3. Internal security measures
As much as external threats pose a risk, internal threats can be just as damaging. A comprehensive security plan should include the following internal measures and be reinforced with comprehensive cloud-based security strategies to mitigate risks from all vectors:
Employee background checks
Before onboarding new employees, thorough background checks can provide valuable insights into their past behavior and reliability.
You can also use an online service or People Search API to look up an SSN to ensure accuracy and thoroughness. It can help mitigate potential risks and protect your company from internal threats.
Regular employee training on security best practices
An employee error can undermine even the most robust security measures. Regularly training employees on security best practices, from spotting phishing emails to safely handling sensitive data, can significantly reduce the risk of unintentional security breaches.
Secure document disposal procedures
Confidential documents should be disposed of securely to prevent sensitive information from falling into the wrong hands.
Implement procedures for shredding or securely erasing sensitive documents and data. Use a reliable Word-to-PDF converter whenever your documents are ready and finalized.
Protection against insider threats
Invest in the best SaaS tools and policies that can help you monitor, detect, and respond to suspicious activities within your organization. It might include segregating duties, limiting access to sensitive information, and deploying insider threat detection software.
Establishing a Business Continuity and Disaster Recovery Plan
Emergencies and disasters are unpredictable, but your response to them doesn't have to be.
A well-crafted Business Continuity and Disaster Recovery Plan (BCDR) can be your company's lifeboat when navigating the stormy seas of unforeseen incidents.
Importance of business continuity and disaster recovery plans
A BCDR plan outlines the procedures and instructions an organization must follow in the face of such incidents.
I cannot overstate the importance of a BCDR plan. It minimizes the impact of disasters on business operations, helps maintain customer trust, and ensures the business's long-term survival.
With such a plan, the company may avoid prolonged downtime, loss of revenue, and in worst cases, complete shutdown.
Steps to create a continuity and recovery plan
- Risk Assessment: Identify the threats and vulnerabilities that could impact your business. Understand the potential impact of these risks to prioritize your planning efforts.
- Business Impact Analysis: Analyze your business processes to identify which are critical to your business's survival. Understand their operational and financial impact if disrupted.
- Resource Identification: Identify the resources required to restore and maintain critical business functions during a disaster, including personnel, information, equipment, financial allocations, and infrastructure.
- Plan Development: Create procedures to manage and recover from the impact of a disaster. Delineate the roles and responsibilities of all involved parties.
- Communication Plan: Develop a communication strategy to inform all stakeholders during a crisis. It includes employees, clients, vendors, and the media.
Testing and updating the plan
A BCDR plan is not a one-and-done project. Test it regularly to identify potential flaws and areas for improvement. Simulated drills and exercises can provide invaluable insights into the effectiveness of your plan.
Moreover, update your plan as your business grows or changes. It includes changes in personnel, processes, technologies, or physical locations. An outdated plan can be as ineffective as no plan at all.
Hiring Security Professionals
Entrepreneurs should consider hiring security professionals, such as GuidePoint Security, when they recognize that the complexity of safeguarding their business assets exceeds their current capacity or expertise.
Staying ahead of potential risks requires specialized knowledge and experience in today's rapidly evolving threat environment. Security professionals can help to:
- Identify vulnerabilities in your current security measures.
- Develop and implement robust security strategies.
- Provide ongoing monitoring and quick response to security incidents.
- Train your team on security best practices.
- Ensure compliance with industry-specific security regulations.
The decision to hire security professionals underscores an important recognition—that the security of your business is a critical aspect of your overall business strategy, requiring expert guidance, ongoing oversight, and proactive planning.
Security is not a “set it and forget it” initiative. With the right partner, you can continuously improve your defenses as your business grows, your systems evolve, and threats become more sophisticated.
Legal and Compliance Aspects of Business Security
Security isn’t only a technical or operational concern—it’s a legal one. Depending on your industry, customer base, and region, your business may be required to follow specific rules for collecting, storing, and protecting customer information.
Compliance also plays a key role in customer trust: when people know you take privacy and security seriously, they’re more comfortable doing business with you.
Understand which regulations apply to your business
Not every business has the same compliance requirements. What applies to you depends on factors such as where your customers are located, what data you collect, and which payment methods you accept. Common examples include:
- Privacy regulations that govern personal data (such as names, emails, IP addresses, and identifiers)
- Payment security standards if you accept credit card payments
- Industry-specific rules (healthcare, finance, education, etc.) if you operate in regulated spaces
If you’re unsure which rules apply, it’s worth consulting legal counsel or a compliance specialist—getting this wrong can be expensive.
Create and maintain clear security policies
Documented policies help your team stay consistent, reduce internal risk, and demonstrate due diligence if you’re ever audited or investigated after an incident.
At a minimum, your policies should cover:
- Who can access which systems and why
- Password and authentication requirements (including 2FA)
- Data retention rules (what you keep and how long)
- Secure handling of customer data and internal documents
- Incident reporting procedures (what to do when something goes wrong)
- Vendor and tool approval requirements
Policies are only effective if they’re followed—so keep them readable, train employees on them, and update them regularly.
Use contracts and vendor reviews to reduce risk
Many breaches happen through third parties—payment processors, analytics scripts, CRMs, customer support tools, and more. Any external vendor that touches your data can become part of your risk surface.
Before adopting a new tool (or renewing a contract), ask questions like:
- What data will this vendor access or store?
- How is the data encrypted (in transit and at rest)?
- Do they support role-based access and audit logs?
- What is their breach notification policy?
- How quickly do they patch vulnerabilities?
- Can you limit data shared with them to the minimum necessary?
Where possible, formalize expectations through vendor agreements and ensure they align with your own privacy policy and obligations.
Maintain proper documentation and audit readiness
If a breach occurs, regulators and customers will want to know what you did to protect data and how you responded. Good documentation helps you prove responsible behavior.
Keep records of:
- Security training completion (who was trained and when)
- Security audits and risk assessments
- Access logs (especially for sensitive systems)
- Patch/update schedules for critical systems
- Incident response drills and improvements made afterward
This makes your business more resilient and reduces the chaos when something unexpected happens.
Prepare for incident response and breach notification requirements
Many privacy laws and contractual agreements require businesses to notify affected users (and sometimes authorities) within specific timeframes after certain incidents.
A basic incident response plan should include:
- How you detect and confirm incidents
- Who is responsible for technical containment and investigation
- Who communicates internally and externally
- How you preserve evidence and logs
- What triggers customer notifications
- How you prevent recurrence
In a real incident, clarity matters more than perfection. A simple plan you can execute is far better than an elaborate plan nobody can follow.
Conclusion
Protecting your business isn’t about paranoia—it’s about preparedness. Today’s risks are physical, digital, and internal, and the businesses that last are the ones that treat security as an ongoing discipline rather than a one-time checklist.
To recap, strengthen your business by:
- Understanding your threat landscape (cyber, physical, internal, and external)
- Implementing strong physical security and access controls
- Maintaining cybersecurity essentials like patching, encryption, and 2FA
- Training employees and reducing internal vulnerabilities
- Building a continuity and disaster recovery plan you can actually execute
- Bringing in security professionals when the risk exceeds your in-house capabilities
- Following the legal and compliance standards that apply to your business
If you take security seriously now—before something goes wrong—you’ll protect your assets, preserve customer trust, and give your business a far better chance of thriving long-term.
Frequently Asked Questions
1. Why is business security important for entrepreneurs?
Business security protects your company’s physical assets, digital systems, customer data, and reputation. Without proper security measures, businesses risk financial loss, operational disruptions, legal consequences, and long-term damage to customer trust.
2. What are the most common security threats businesses face?
Businesses commonly face cyber threats such as phishing, ransomware, and data breaches, as well as physical threats like theft and vandalism. Internal threats—such as employee errors or the misuse of sensitive information—and external threats —such as fraud or corporate espionage — can also pose serious risks.
3. How can small businesses improve their cybersecurity?
Small businesses can strengthen cybersecurity by keeping software up to date, using firewalls and antivirus protection, enabling two-factor authentication, encrypting sensitive data, and training employees to recognize phishing attempts and other common cyber threats.
4. What is a business continuity and disaster recovery plan?
A Business Continuity and Disaster Recovery (BCDR) plan outlines how a company will continue operating during unexpected disruptions and how it will restore normal operations afterward. It typically includes risk assessments, recovery procedures, communication plans, and regular testing to ensure the plan works effectively.


