You may think that hackers and cybercriminals only target big corporations.
The truth is, criminals attack small businesses, too. In fact, they may see smaller businesses as easier targets because of the typical lack of adequate security measures.
Studies show that 1 in 5 small businesses doesn’t have an effective cybersecurity plan.
To ensure the security of your overall small business and customer data, you need to conduct a security audit. What is a security audit, and how is it done? Here’s a guide for your small business.
In this article:
- Why Regular Security Audits Are Important for Business
- Types of Security Audits
- How Often Should You Perform Security Audits
- How Much Do Security Audits Cost?
- 4 Key Steps to Conducting a Security Audit
What Is a Security Audit?
A security audit evaluates a company’s information systems against a set of criteria to assess their security.
This criterion is usually a checklist of industry best practices, federal regulations, and external standards.
The security audit evaluates your business’s defenses across the following areas:
- Network Vulnerabilities - These are non-physical security threats related to organizational software and data, including Kubernetes security measures for containerized applications. The security audit checks for weaknesses and potential breach points in your network's firewall configurations and public and private access points. It should also evaluate how traffic is routed through how a content delivery network works, as strategically distributed edge servers can curb latency and deflect certain attack vectors.
- Physical Components - This is the environment or infrastructure that houses your business information systems. The building should be as secure as the networks and software.
- User Practices - This is the human dimension of a security audit. The audit checks how staff members collect, share, and store sensitive business and customer data.
- Overall Security Strategy - This refers to your overall business security policies that protect your data from potential security breaches.
As a small business owner, you can choose whether the security audit is conducted internally by your security team or by a third-party security expert. You can also choose how often the audit will be done. We’ll talk more about this later.
Why Regular Security Audits Are Important for Business
Now that you know the answer to the question, “What is a security audit?” let’s talk about why it’s important for your business. Regular security audits help ensure your business is compliant with regulatory requirements.
For example, routine audits allow your business to comply with the General Data Protection Regulation (GDPR). This law helps protect EU user data from security breaches when they transact online.
Audits help you identify whether you’re compliant with the required encryption and data storage regulations to avoid hefty GDPR fines.

Source: The Conversation
Regular audits also help elevate your business’s security posture. The audit helps you identify potential security risks before they are discovered by cybercriminals.
Beyond digital threats, comprehensive audits should also assess physical security technologies, such as AI gun detection, that can prevent workplace violence incidents from escalating.
An audit can also help you configure network automation technology to continuously monitor for breaches. It is less costly to conduct regular security audits than to deal with cyberattacks or data breaches.
The average cost of addressing a data breach in the US is a whopping $9.44 million.
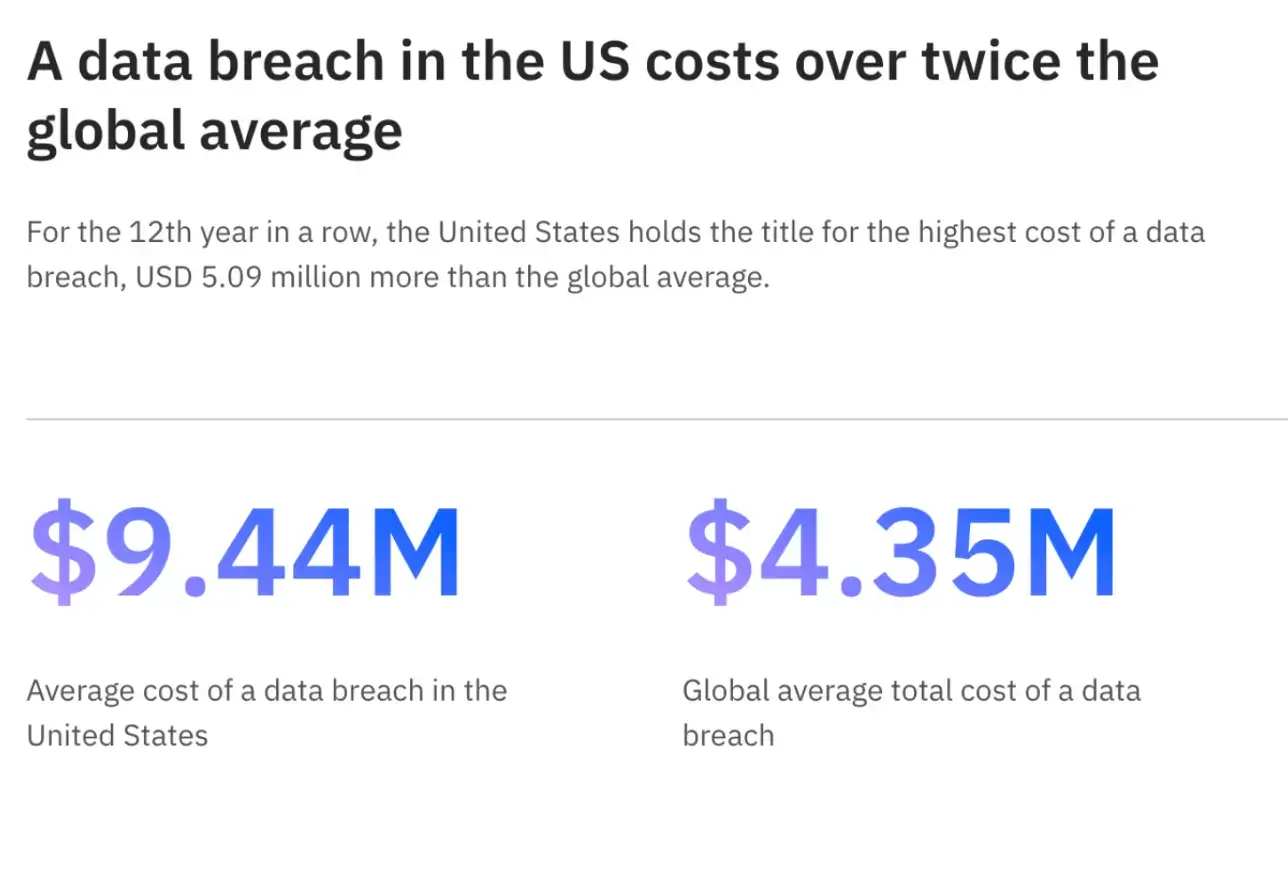
Source: Medium
This is a high price to pay, especially considering that it is preventable. Other consequences of cyber attacks and security breaches include loss of customer trust and damage to reputation.
They are an opportunity to identify areas where additional employee security training is required, which can often involve specialized learning programs such as a Cybersecurity Bootcamp.
They also allow you to create new security policies to address any emerging security threats.
Ultimately, security audits are a great way to persuade consumers that you take their data security seriously. The result is that they transact with you.
Alternatively, you can invest in a DSPM tool to gain full visibility into your organization's data, helping to reduce security risks and maintain compliance without operational overhead.
Types of Security Audits
- Internal audits
- External audits
As mentioned earlier, there are two main types of security audits you can conduct for your business.
Internal audits
An internal security audit is conducted by your employees. It gives you more control over what is audited and who will undertake the process.
You also get to determine how much money and time will go into the audit process.
If you opt for this, make sure you give your team the resources they need. For instance, if you want them to test the security of your information systems, you can give them access to ChatGPT for hacking purposes.
Other tools they might need include antivirus software systems, a firewall, and penetration testing tools.
External audits
An external audit is conducted by an organization with no affiliation to your business. It is a good way to get unbiased results that will help you make objective decisions concerning your business’s security.
Third-party security firms, for instance, may highlight and mitigate any generative AI risks your business may be exposed to while using OpenAI and other modern technology tools.
This is something your internal team might not be able to uncover since they may be biased toward the tool your company has been using for a long time.
Federal regulations like FedRAMP require an external audit before they give you a certification for your business.
Each audit type should assess different aspects of your cybersecurity framework. For detailed insights into these layers, refer to the 7 cybersecurity layers by ZenBusiness.
While you can conduct an internal audit, a third-party audit is necessary. Overall, here are the main differences between internal and external audits.
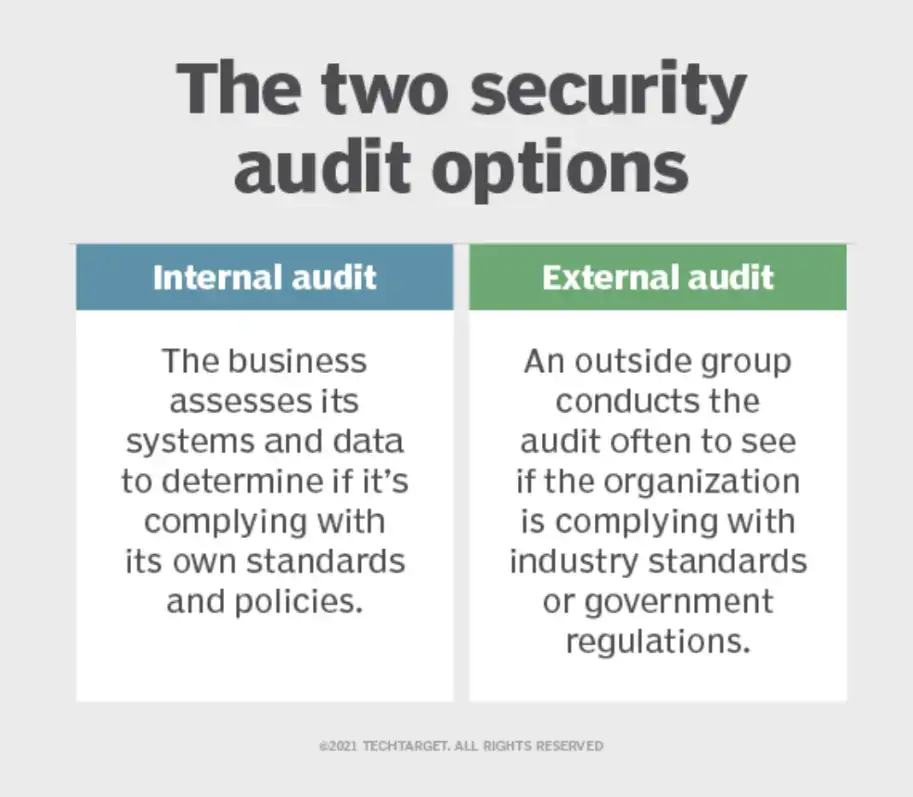
Source: TechTarget
If you have the budget, consider leveraging both types of audits for your business. This will help ensure your company's systems are foolproof.
How Often Should You Perform Security Audits
How often you perform security audits for your small business depends on:
- Size of the business
- The kind of data you handle
- Types of security tests you run
If you have a growing business with several interconnected departments, you’ll need more frequent audits than you needed when you were starting. This is because each new department can be a point of vulnerability for security attacks.
How often you perform security audits also depends on the security risks your small business faces in its daily operations.
If you’re an eCommerce business that gets customers’ financial information online during every purchase, for example, you’ll probably need to run security audits more frequently than if you were a brick-and-mortar store that uses its website only to showcase its products.
For example, risk and vulnerability assessments can be conducted quarterly or monthly, as they are not time- or resource-intensive.
However, penetration testing is typically done annually or biannually because it’s more complex and requires more resources.
While it’s standard to conduct security audits annually or biannually, you can increase their frequency depending on the factors above.
How Much Do Security Audits Cost?
A security audit can cost you anywhere up to $2500. Several factors determine the cost of a security audit.
First, the size of your business and the complexity of your information systems. Larger, more complex businesses require more time and expertise to ensure a comprehensive audit.
The types of tests you wish to conduct also determine the overall cost of the audit. For instance, as I said earlier, a penetration test, which involves more steps, is more expensive than a simple risk assessment.
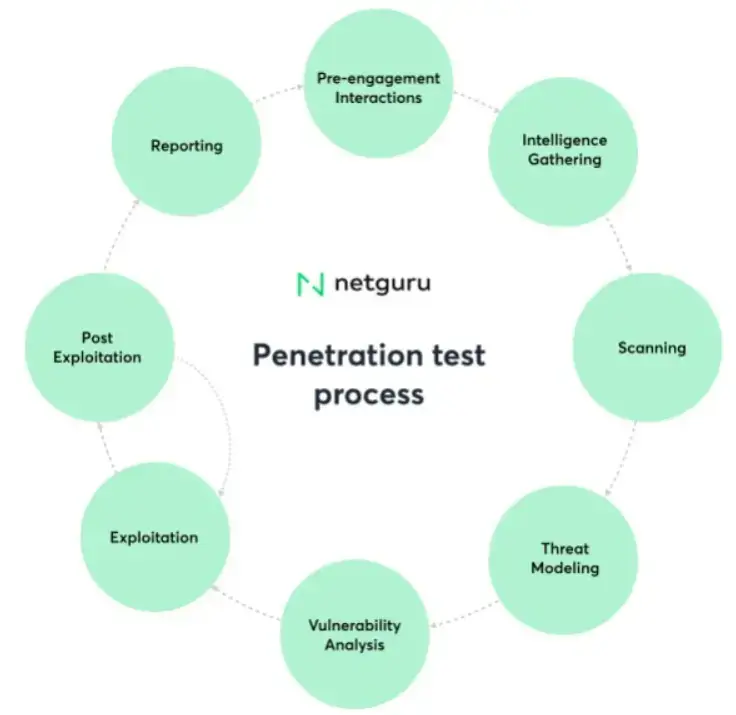
Source: Netguru
A risk assessment, meanwhile, can even cost you virtually nothing (if you do it yourself, for example). This brings us to the third factor that determines the cost of a security audit: who does it.
Of course, you’ll end up saving on costs if you let your own team conduct the audit. Hiring a third party to do it for you will incur more expenses. These firms can charge an hourly fee or a flat rate.
4 Key Steps to Conducting a Security Audit
- Planning
- Preparation of documents
- Testing
- Reporting
Here are four steps that need to be followed for a comprehensive security audit:
1. Planning
The first step is to craft an audit plan for your business. Create an outline of the objectives of the security audit, its scope, and the tools or techniques needed to complete those tasks.
If you hire a third party, they may create the audit plan themselves and present it to you. When they do, make sure their plan shows that all potential vulnerability points are covered by the audit.
2. Preparation of documents
At this stage, the auditors—your internal team or an external party—are preparing to conduct a security check of your business. Give them all the necessary information about your business’s existing infrastructure and information systems.
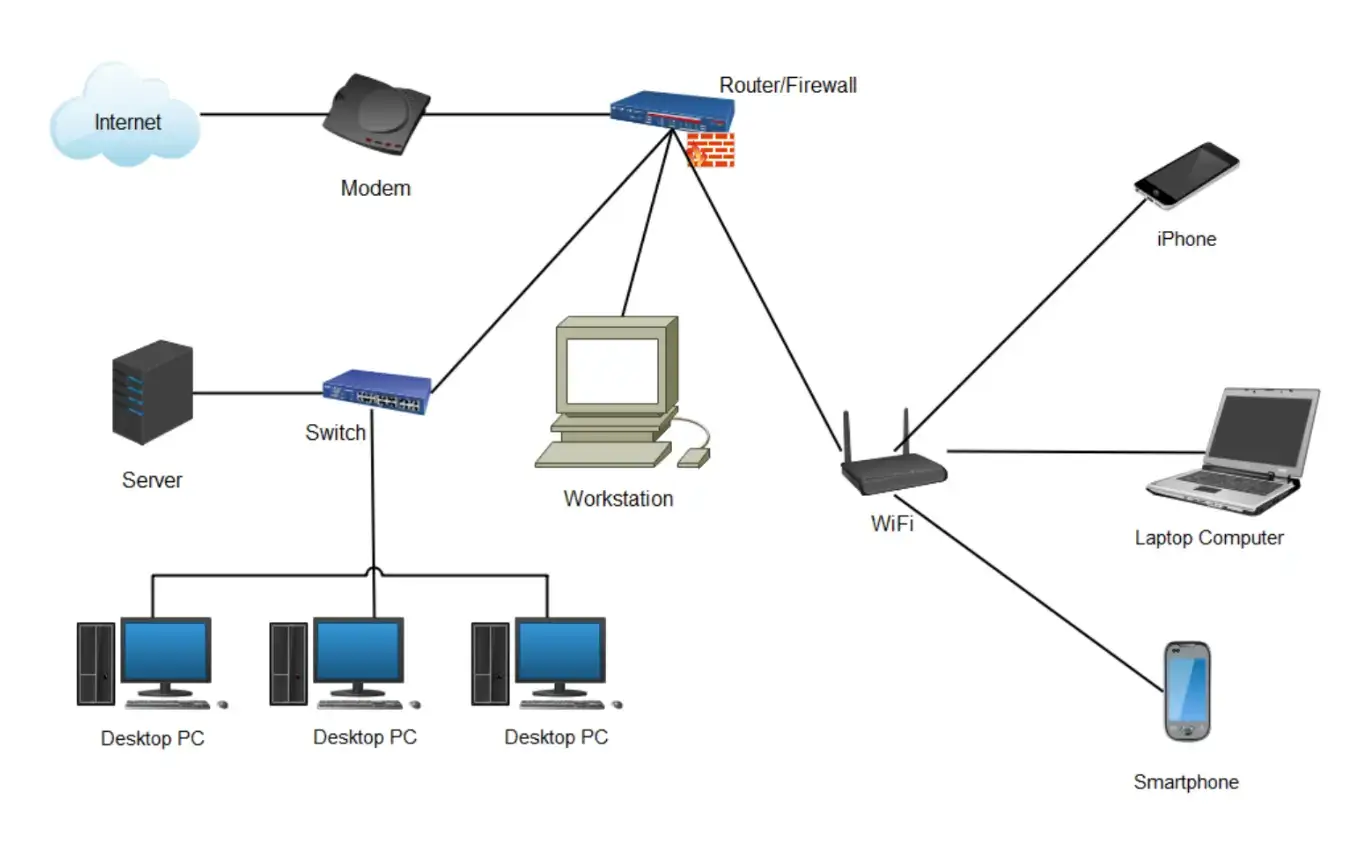
Source: Edrawsoft
Some of the data you should give them includes your security strategies and policies, system logs, and network diagrams, such as the one above.
3. Testing
This is where the rubber meets the road. Security experts will conduct the audit in accordance with the plan developed.
How long the testing takes will depend on the scope of the security audit determined at the beginning of the process. Either way, this may last for days to weeks, so you might want to schedule it when business is slow.
4. Reporting
Finally, the security auditors will compile all their findings into a report. The report will also include the interventions they recommend to keep your business safe from security breaches.
You can ask the auditors to use a data visualization tool to create graphs and tables for the data. This will make the report easier for readers to comprehend. You may also ask them to present their audit findings to management and other concerned staff.
Conclusion
What is a security audit? It’s a process that helps businesses evaluate the security of their information systems and networks.
An audit ensures regulatory compliance and boosts client trust in your business. It also helps you save on the potential cost of addressing a security breach or cyberattack.
You learned other important things about security audits in this article.
The two main types of security audits are internal and external audits. You can decide how frequently you’d like to audit your business depending on your unique needs.
The cost will also depend on the nature and scope of the audit you intend to conduct. Meanwhile, to conduct the audit, you learned that planning, documentation preparation, testing, and reporting are key.
With all this information, you are now equipped to get an effective security audit done for your business.

Author Bio
Dillon Deckard is a seasoned content writer at StationX with over 7 years of experience in cybersecurity. He has a knack for finding fresh ideas and is always eager to learn new things. He is passionate about sharing actionable insights through his approachable blog posts, which are designed to empower marketers at all levels. You can find him on LinkedIn, where he is always open to networking and connecting with industry professionals.


